Part 1: The Artifact
Analysts, We have successfully decrypted the root folder of the hard drive seized from Asset Echo prior to his disappearance in September 2017.
The drive contained a single image file titled meet_loc.jpg.
Intelligence indicates that Echo used this specific image to communicate a meeting point to his handler. However, standard geolocation attempts have been inconclusive so far. We suspect this is not a simple photograph; Echo was known for altering images within his communications to avoid detection.
Perform a full analysis of the attached file. We need to know exactly where Echo was heading. Everything you need to find the location is contained within this file. All we know so far is that the location was a hotel in London.
You need to find the specific hotel that Echo went to.

I started by uploading the image into Forensically, a browser-based image forensics tool that lets you dig into things like metadata, noise analysis, and hidden layers that wouldn’t be visible to the naked eye.
The first thing that caught my eye was a strange string buried in the metadata:
| Embedded Metadata |
|---|
| I swim in silver schools, yet I am named for a crimson hue I only acquire after death. I have no legs, yet I am famous for leading hounds astray. What am I? |
I wasn’t sure what to make of this riddle at first, but something felt off about it. I threw it into an AI and the answer came back as a Red Herring. Literally. A classic piece of misdirection, designed to waste your time chasing something that leads nowhere. I moved on.
I kept digging through Forensically, adjusting the opacity slider to try and reveal anything that might be layered or hidden within the image. It’s a technique used to detect composited elements or faint overlays that don’t show up under normal viewing. After some persistence, I spotted three seemingly random words faintly visible at the top of the image.
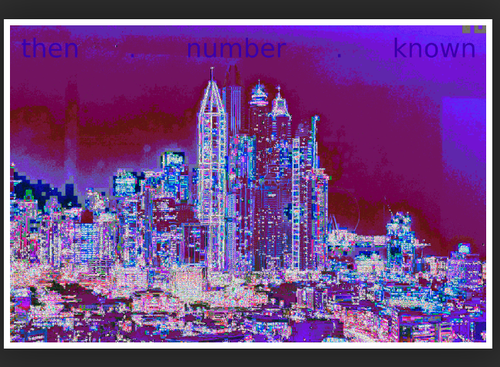
At this point I was stumped. Three random words, no obvious meaning, no immediate connection to anything. I stepped away from the laptop.
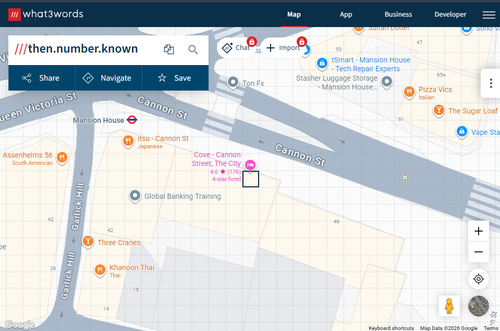
An hour or two later I was on the couch watching TV, but my brain wouldn’t let it go. Then it clicked, a previous Hacktoria challenge had introduced me to something called What3words. What3words is a geocoding system that divides the entire surface of the Earth into 3m x 3m squares, and assigns each one a unique combination of exactly three words. It’s used for precise location sharing emergency services, deliveries and navigation anywhere a traditional address isn’t specific enough. Those three words weren’t random at all. I ran to the laptop, jumped onto What3words, typed in the three words, and landed on The City Hotel on Cannon Street, London. Echo’s meeting point, confirmed.
Part 2: The Getaway
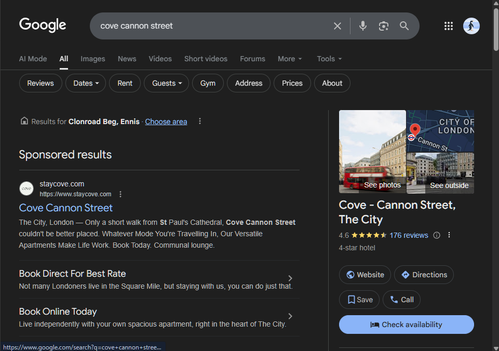
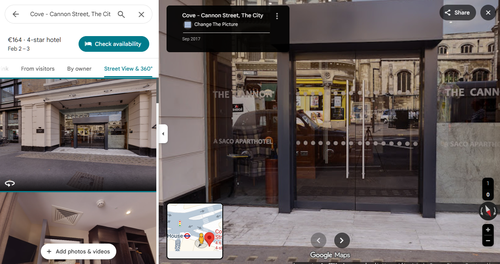
Excellent work! The location is confirmed: Cove Cannon Street.
We know Echo arrived at this location in September 2017, but local CCTV from that day was wiped long ago. We must rely on open-source intelligence to reconstruct the scene.
Intel indicates Echo was extracted by a London black cab waiting directly outside the hotel entrance. To track the vehicle, we need its registration number.
Scour historical imagery from around the hotel from that specific timeframe (Sept 2017). We believe a civilian may have captured a visual of the vehicle. We can search any license plates identified to see if anything flags up in our databases.
Find the taxi and report back on the license plate.
DISCLAIMER/UPDATE: The visual you need turns out to be taken from Aug 2016, but nonetheless it was UPLOADED in Sep 2017. If you find the visual and notice "Aug 2016", don't be discouraged.
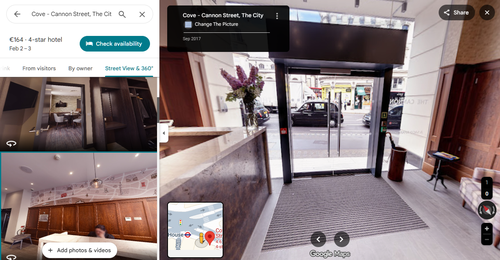
With the hotel confirmed I went straight to Google Maps and searched for Cove Cannon Street. I navigated to the Street View & 360 section on the hotel listing and filtered to visitor uploaded images from September 2017. Google Maps allows you to browse 360 degree walkthroughs uploaded by visitors, including ones with timestamps, which makes it a useful tool for reconstructing what a location looked like at a specific point in time. I found a September 2017 upload and started navigating through it. The walkthrough started outside on Cannon Street, and I worked my way inside through the hotel entrance.
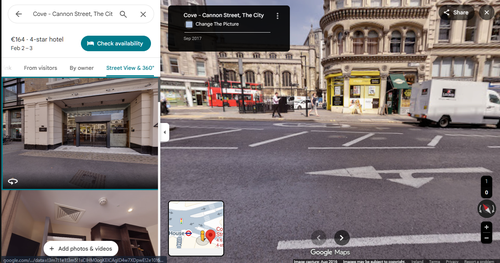
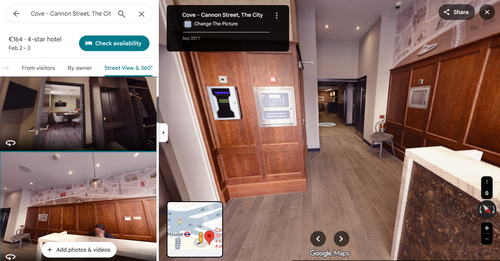
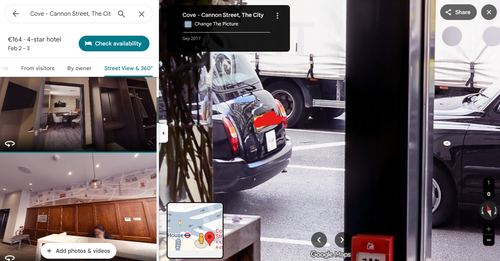
Once inside the lobby I turned back towards the front door and looking out through the glass I could see a black cab parked directly outside.
I zoomed in and the registration plate was clearly visible.
Part 3: The Odometer
Target vehicle identified: GX57 CPK (London Black Cab).
Analysis confirms the driver is a known associate of Echo, retained to facilitate movements throughout late 2017.
We have seized personal maintenance logs from the driver's residence which claim the vehicle was sitting idle during the weeks following the drop. We need to verify the veracity of these claims against official data.
Locate the officially recorded mileage for this vehicle from October 2017. We will cross-reference your findings against the seized logs to confirm the driver's timeline.
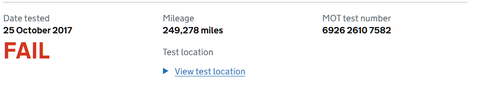
The UK government provides a free public tool for checking a vehicle’s MOT history, including recorded mileage at each test. I headed straight to the GOV.UK MOT History Checker, entered the plate GX57 CPK, and pulled up the full MOT history for the vehicle. The October 2017 MOT entry listed the officially recorded odometer reading, giving us a verifiable data point to cross-reference against the driver’s maintenance logs.
Part 4: The Key Source
Agents,
Our cryptanalysis team has finally managed to bypass the encryption on the final folder of the 'Echo' drive.
Inside, they found a text file containing a string of scrambled characters and a set of instructions. It appears Echo used a manual encryption method to secure his final message, relying on a specific keyphrase to lock it.
The instructions point to a physical 'Key Source' that existed publicly at the time of his disappearance.
Key Source Intel:
Publication: Hackney Today
Date: 25 September 2017
Location: Page 8
Intelligence indicates the key is a 'well-known phrase' found on this page. We need you to identify this phrase so we can attempt to decrypt the message.
Find the publication and locate the phrase on page 8.
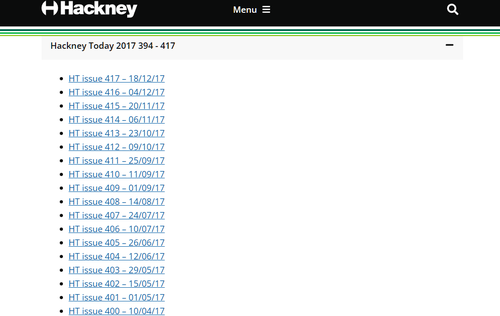
The brief pointed to a specific issue of Hackney Today, a free local newspaper published by the London Borough of Hackney. The first task was actually finding a copy, a September 2017 edition of a local council newspaper isn’t exactly sitting on Google’s front page. I tracked down the Hackney Council Publication Archive, which hosts archived issues going back several years. The archive was organised by issue number, so I located Issue 411, dated 25 September 2017 and opened the link.
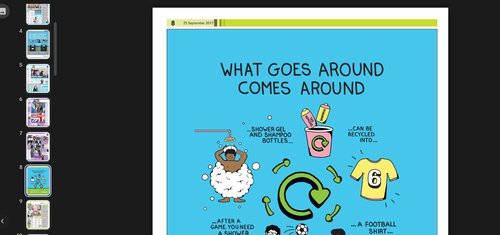
This brought me to a Google Drive hosted PDF of the full issue. I navigated straight to page 8 and immediately spotted a full-page recycling infographic with the phrase printed in large bold text as the headline title:
Part 5: The Cipher
We have the key. Now we can proceed to the message itself.
Below is the ciphertext extracted from the file. We do not know which specific cipher algorithm Echo used, but we know it relies on the text-based key you identified in the previous step.
Intercepted Ciphertext: WZSXZQSEPICGVVGRMFGRK
Analyse the ciphertext. Determine the encryption method used. Use the key from Challenge 4 to decrypt the string and reveal Echo's final status.
This is the end of the line, Agents. Good luck.
The first step was figuring out which cipher Echo had used. I headed to dcode.fr and used their Cipher Identifier tool, pasting in the ciphertext WZSXZQSEPICGVVGRMFGRK. The tool analysed the string and returned Vigenere Cipher as the top result.
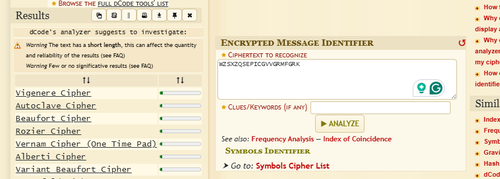
I switched to the Vigenere Decoder on dcode.fr, entered the ciphertext and along with the key WHATGOESAROUNDCOMESAROUND, and ran the decryption.
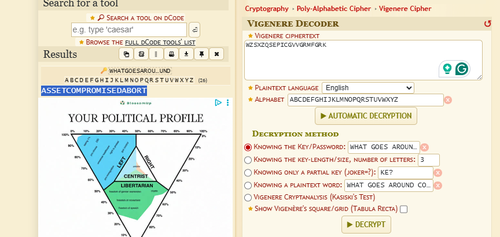
ASSETCOMPROMISEDABORT
Echo’s final message decrypted. Asset Echo had been compromised and the operation was aborted. Case closed.

Comments
Be the first to start the conversation.
Leave a Comment